Prodotti in vetrina
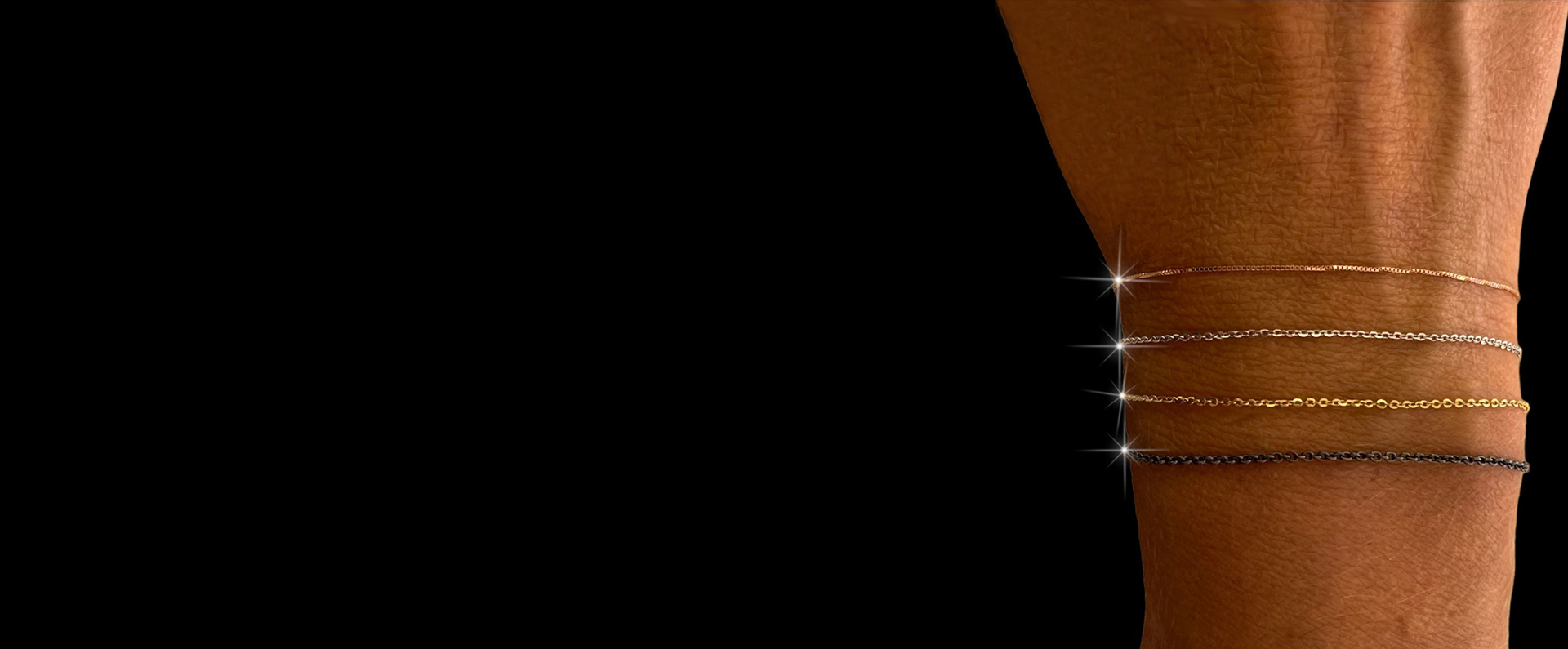
Bracciale Argento in Filigrana sarda
Bracciale filigrana sarda, interamente realizzato a mano
86,00 €
Sconto:
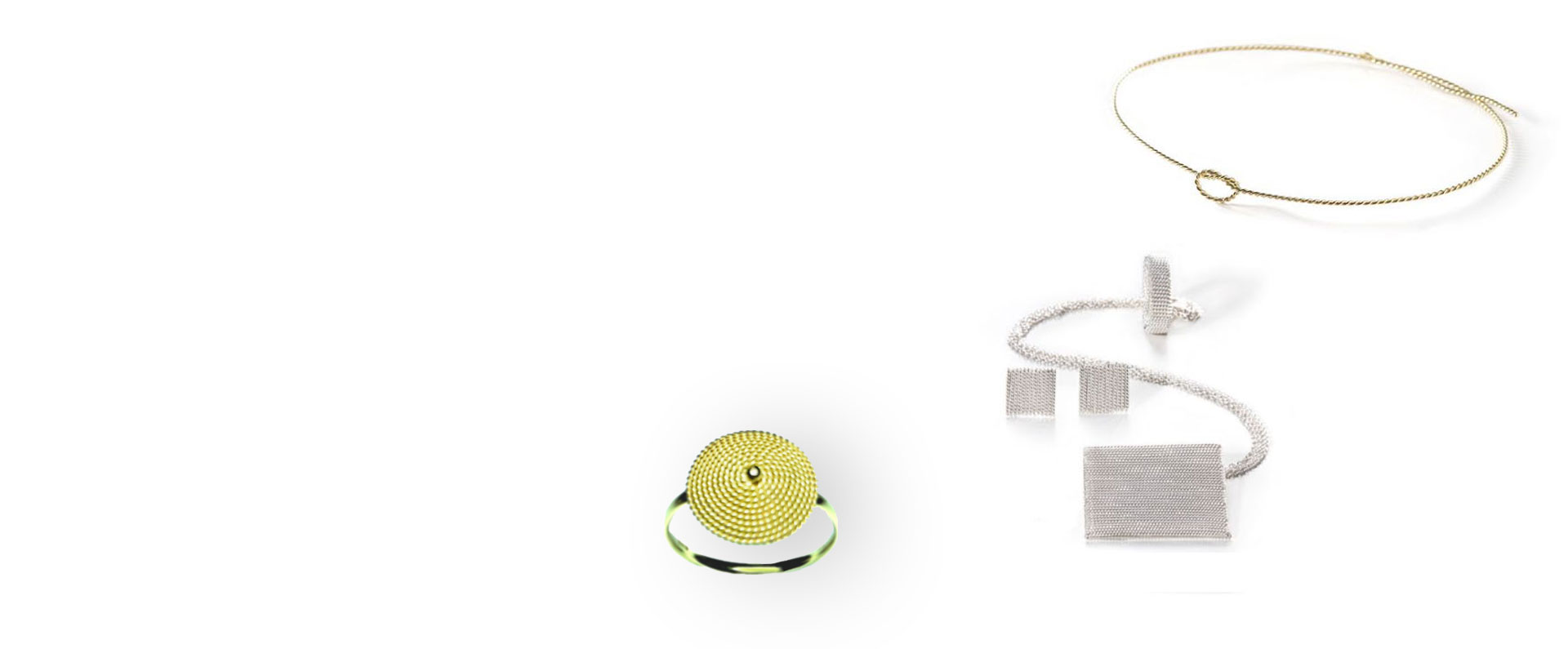
Anello Filo della Vita in argento 925
Anello in argento, realizzato interamente a mano.
10,00 €
Sconto:
Bracciale Argento in Filigrana sarda
Bracciale filigrana sarda, interamente realizzato a mano
76,00 €
Sconto: